Replay Attack
Introduction
Every SSO protocol provides freshness parameters N to limit the reuse and lifetime of the authentication tokens. Taking into account that the reuse of tokens is optional, the validation of the attributes providing freshness is not considered as critical. On the other hand, the time restriction regarding the usage of authentication tokens is more critical and should be evaluated. Otherwise, tokens issued once might be valid for an extended time period or even an infinite amount of time.
Attack subtypes
There are no attack subtypes for this attack.
Prerequisites
The attacker needs access to a valid token. More specifically, the token in question is required to be valid for the Software-as-a-Service Cloud Provider (SaaS-CP) at any time in the past. This can be achieved if the attacker had legitimate access (for a limited period of time) to the SaaS-CP via SSO and used this access to generate and store a token for himself. Alternatively, searching for published tokens in forums or in technical documentations could also provide valid, though most possibly outdated, tokens.
Target
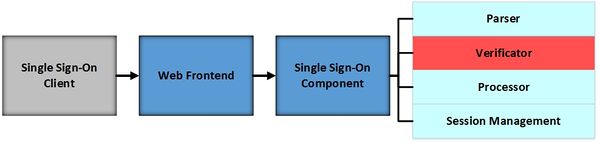
The attacked Single Sign-On component is marked in red colour.
Description
The attacker sends an expired authentication token to the target SaaS-CP. In case, that the unlimited reuse of authentication tokens is applicable and the token is successfully verified, the attack is classified as successful. The attack’s impact is average since the attacker has limited attack surface – he can only spend authentication tokens he possesses. However, the potential impact drastically rises in case the attacker gains hold of an authentication token granting him extended access rights (e.g., as an administrator of the system).
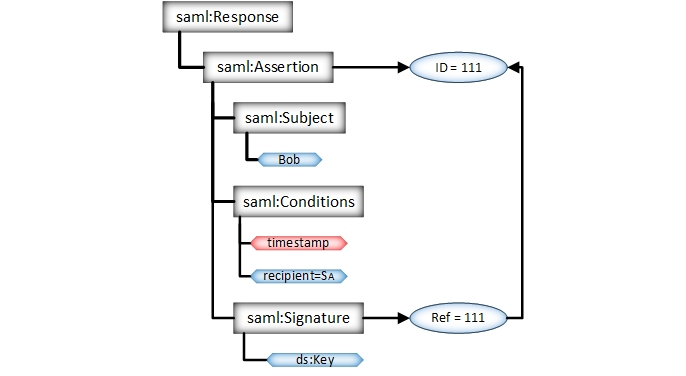
SAML token with expired timestamps is sent to the SaaS-CP.
As can be seen in the example bellow, a SAML Response can contain several timestamps:
- Response:IssueInstant
- Assertion:IssueInstant
- SubjectConfirmationData:NotOnOrAfter
- Conditions:NotBefore
- Conditions:NotOnOrAfter
- AuthnStatement:AuthnInstant
Thus, the timestamp validation logic is not simple. The implementor needs to pay close attention to the NotOnOrAfter attributes and also make sure, that the SAML Response matches the correct previous Request (SubjectConfirmationData:InResponseTo).
<samlp:Response
...
IssueInstant="2015-12-05T09:22:05">
...
<saml:Assertion
ID="111"
...
IssueInstant="2015-12-05T09:22:05">
...
<ds:Signature>...</ds:Signature>
<saml:Subject>
<saml:NameID
...>
Bob
</saml:NameID>
<saml:SubjectConfirmation
Method="urn:oasis:names:tc:SAML:2.0:cm:bearer">
<saml:SubjectConfirmationData
InResponseTo="request_1"
Recipient="https://sp.example.com/SAML2/SSO/POST"
NotOnOrAfter="2015-12-05T09:27:05"/>
</saml:SubjectConfirmation>
</saml:Subject>
<saml:Conditions
NotBefore="2015-12-05T09:17:05"
NotOnOrAfter="2015-12-05T09:27:05">
...
</saml:Conditions>
<saml:AuthnStatement
AuthnInstant="2015-12-05T09:22:00"
SessionIndex="session_3">
<saml:AuthnContext>
<saml:AuthnContextClassRef>
urn:oasis:names:tc:SAML:2.0:ac:classes:PasswordProtectedTransport
</saml:AuthnContextClassRef>
</saml:AuthnContext>
</saml:AuthnStatement>
</saml:Assertion>
</samlp:Response>Mitigation / Countermeasures
This component should validate attributes providing the corresponding restrictions, i.e., the freshness parameter N. In the SAML context relevant to this study, this parameter is represented by NotOnOrAfter and NotBefore. Failing to properly verify these parameters will enable this attack type. Another possibility to enable this attack type would be via additional freshness attributes, which are not part of the digital signature s.
Practical Examples
In 2014, Mainka et al. analyzed 22 Software as a Service cloud providers and found out, that different frameworks were vulnerable to this attack: Clarizen, Instructure, AppDynamics, TimeOffManager, LiveHive and CA Service Management.
References
C. Mainka, V. Mladenov, F. Feldmann, J. Krautwald, J. Schwenk (2014): Your Software at my Service: Security Analysis of SaaS Single Sign-On Solutions in the Cloud. In The ACM Cloud Computing Security Workshop (CCSW).
- Pages using deprecated source tags
- Pages with syntax highlighting errors
- Attack Categorisation By Attacker Model: Access to Valid Token
- Attack Categorisation By Violated Security Objective Access Control
- Attack Categorisation By Attack on IdP/ SP: Attack on SP
- Attack Categorisation By Attacked Web Service Component: Signature Verification
- Attack Categorisation By Attack Spreading:Application Specific Flaws
- Attack Categorisation By Attack on SAML